Copper Theft | Preventing Copper Theft | Copper Theft and RI Businesses
Copper Theft

Copper is so incredibly useful that millions of households around the world rely almost exclusively on copper wire to transfer power from one source to another, including automobile batteries and even outdoor lighting. In short, copper is everywhere and in need almost everywhere.
However, there is another side to the copper story. As the price of copper has been rising, so have copper thefts. Thieves know that if they can strip wiring out of a building, from a transformer, motor, or a vehicle, the copper within the wiring is a valuable commodity.
Question: Why are copper thefts in the United States on the rise?
Answer: Copper is sometimes referred to as “Doctor Copper”, because it is the only metal with a Ph.D in economics. Traditionally, because copper cabling is used in the construction, electronics, and automotive industries, it is a key bellwether of the economy; viewing a simple graph of copper prices can give you great insight into business conditions. However, with the Federal Reserve printing $4T of money last year, and expected to print $4T or more in 2021 (with much of it for infrastructure – which copper is a key input to), the effect on Copper is not only via the stimulated economy; there is now the prospect of significant inflation, which is affecting copper prices, on top of the increased economic activity driving higher demand. As a result, we expect over the next several years that copper theft will be on the increase, and companies will be on the lookout for ways to protect their copper cabling.
Copper theft is the theft of non-financial objects destined for use in communications or other electronics, made of metal. Since copper is a valuable metal, theft of it has become a business for transnational organized crime syndicates. Metal theft is also known in the black-market trade.
Question: How to Prevent Copper Cable Theft?

Answer: The way to prevent copper wire theft when working with these cables is to secure the job site against theft. There are several approaches you can use to stop copper thieves, all involving physical security measures.
A. You can outsource to a security company such as SecurityRI. The professionals can station a security officer at the job site location, where the copper is held. This works for all locations, where a thief can access the wire. The security officer’s conduct random rounds of the location, to ensure they are monitoring the property and reducing any breaches.
B. Surveillance cameras can reduce copper theft by establishing a deterrent, while recording any breaches. Surveillance cameras are better used if your business or security company receives alerts. The alerts will assist with avoiding the theft, instead of dealing with the consequences. Cameras are a great method of protecting copper in remote locations.
C. Access control – ensure your location has proper access control, therefore you can avoid any unwanted guests. Access control will work as a deterrent as well. When thieves know your property is guarded buy a security officer, surveillance cameras and access control – there’s a good chance the thief will target another location.
Learning how to prevent copper theft in an apartment, building, or business is something that should be taken very seriously. There are many cases of copper wire being stolen in many different ways. In some cases, criminals dig up old infrastructure or underground piping to gain access to wiring. While there is no way to stop copper theft completely, there are things that an owner can do to minimize his risk.
How to prevent the theft of copper wire begins with proper shielding and sealing. All wiring should be properly installed and run through safety test and maintenance. It is also a good idea to find an experienced electrician who has plenty of experience installing all types of wiring in both commercial and residential buildings. They should be licensed and bonded and have extensive knowledge of copper and its insulating properties.
Knowing how to prevent copper theft in an apartment or building goes beyond locking up your valuables and securing your property.
Many buildings have a policy regarding what type of lights and decorations are allowed in the common areas. If an apartment has a pool, security cameras may be installed. These cameras are great for monitoring security in an apartment complex or building, but they may not identify potential thieves. A security camera with a clear visor is the best option for identifying perpetrators of copper theft. Keeping these areas well lit is a good idea for property owners, because if the thief is wearing bright clothes or carrying a torch, it can confuse a surveillance camera.
One of the most common methods on how to prevent copper theft in an office building is through the installation of anti-theft devices. Often, security companies that track down perpetrators will check to see if these devices are installed properly. For instance, a burglar who tries to steal copper wiring will bypass a security company’s alarm, because they know that the alarm will not go off if the wiring is cut. It is therefore very important to check to make sure that all wires and cabling are connected properly.
An office that has multiple floors also has an increased risk of theft. Since there are more floor sections in a building, it becomes harder to prevent the crime from occurring. Security companies can install cameras and other items that will help to monitor the area. Keeping the area well lighted is important when trying to prevent this type of theft in an office setting.
Prevention is often the best form of defense against such crimes. If an office suspects that theft is happening, it should contact a security firm immediately. Copper is costly and the material is used for very high-end products in offices, so the temptation to take it could be very powerful. A good theft deterrent is a good prevention tool.
Question: How to Reduce Copper Theft?

Answer: How to reduce copper theft in piping comes down to prevention.
The first step to take when thinking about preventing copper theft in water is to think about who is responsible for maintenance. Some companies will fit replacement pipes, while some will just repair damaged piping.
When pipes are leaking, they should be repaired immediately to avoid further damage. In addition to this, any leaks that occur should be repaired right away – otherwise you run the risk of contaminating the surrounding water supply. Leaking copper piping can also affect the general condition of your water system. When you see copper running across the water mains or through the plumbing system, you should get people to bring the water back up to a normal state as quickly as possible.
When you are considering how to reduce copper theft in a water piping system, you need to think about the physical conditions around the system. For example, copper piping that is close to the ground will be more likely to be picked up and sold than those that are closer to the surface.
Question: What is Copper Theft?

Answer: Copper is one of the most widely used elements in modern industry. It is used in electronics, electric appliances, dental work, military equipment, and so on. The demand for copper is increasing as rapidly as other materials that have become valuable on the global market, like oil, gold, silver, platinum, and others.
Copper can be stolen from electric power lines. It can also be stolen through unplugging a device in order to gain access to its circuit board.
Question: Why Copper Theft is a Problem

Answer: It is a big problem because without copper wire, our modern world would be almost impossible. Communication is a big part of modern society. Without electricity, you would not have cell phones, computers, microwaves, or telephones.
Another reason why copper theft is a problem is that it hurts the economy. Copper is one of the most important minerals used in modern industry. Copper is used in everything from electronics to medicine to dentistry. In short, without copper, modern industry as we know it would not exist.
Inflation and Copper Prices
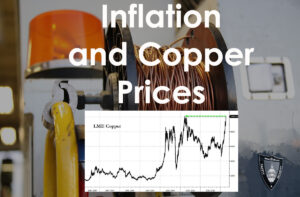
It seems that the economic and political fallout from the global credit crisis will drive up copper and other metals, as well as fuel prices, which often lead to inflation and price increases. In a time when so many people are reeling from the effects of the recession, this can be very dangerous for the economy. With unemployment on the rise and consumers tightening their belts, it is important to remember that the price of essentials such as food, fuel and copper is necessary to provide a decent standard of living.
How does inflation factor into copper and other metals? Generally, inflation tends to take its toll on investment and trade. With increased costs, demand decreases, and the economy remains sluggish. As consumers tighten their belts and look for cheaper sources of energy and basic goods, the cost of essential items such as copper begins to increase. When the price of copper or other metals rises, this naturally drives up commodity prices as well.
Naturally, copper, and other metals are sold in large quantities during times of high inflation, such as today. The high prices of these metals act as an effective brake on new supply growth. Investors and traders try to ride out the inflation cycle by holding onto their investments. When the prices of copper or other commodities rise, they sell at higher prices, offsetting the higher inflation cost on those metals. Consequently, the overall effect on the prices of copper, iron, and other metals remain positive.
As you can see, there is a delicate balance that is required in determining the market price for copper. If the economy expands, then the cost of copper should go up. Conversely, if the economy contracts, then copper prices should fall. However, inflation, although important to the metal market, is not considered by investors in the same light as the stock market, real estate, or commodities.
Copper Thieves

When we talk about copper thieves and copper wire thieves we are talking about the same thing. These are the people who steal copper wire in order to sell it or to replace it. In this case they are also stealing the valuable metal and in fact, they are stealing from everyone. There have been instances of people being inadvertently killed by electrocution because they were stealing copper wire. The thieves do not only target copper wire, but they may try to steal any other metal including steel wire, brass wire, fiber optic wire and even telephone wire.
Question: How to Secure Copper From Theft?

Answer: If you own a business that has the need to secure copper wiring or have employees that handle this type of valuable metal, you know how difficult it can be to find out how to secure copper from theft. Most businesses and organizations have experienced enough loss and damage to know how serious it is when it comes to copper theft protection. However, there are some simple measures that you can take to reduce copper theft while avoiding the expensive and often-time unnecessary expense that this type of theft creates.
The most obvious step to take if you are wondering how to secure copper from theft is to install security measures. There are several ways to protect your assets, but not all of them are effective. For instance, you may want to install video surveillance equipment in and around the premises. This can provide proof to a potential thief that they will likely never see coming. Of course, if you are in a public building, such as a bank, you should consider the option of using an alarm system as well.
It is a good idea for how to secure copper from theft to find a company that can provide you with the best protection. For example, if you want to protect all of your property from theft then you should look for a company that offers a full protective service.
Finding a reputable security services company that can offer you how to secure copper from theft is important for protecting your valuable property. If you need to protect the wiring that runs across your entire building from damage and theft then you will want to choose a company that has experience in providing this type of security. Look for a company that offers protection from all forms of theft, not just copper theft.
For a free security analysis please contact us here at SecurityRI: